XML is the primary format used by IdentityIQ to store and exchange data. It is essential to understand how to query XML data from IdentityIQ tables as this one skill could significantly expedite the process of extracting information from IdentityIQ and save you hours during troubleshooting or while performing data analysis. In this article...
Continue readingAdopting agile methodology in your SailPoint-enabled IAM program
Identity and Access Management (IAM) is a crucial component of any organization’s security strategy, and adopting an agile methodology can greatly improve the speed, effectiveness, and overall success of your SailPoint-enabled IAM program. By breaking down projects into smaller, manageable tasks called sprints, and emphasizing collaboration, flexibility, and adaptability, Agile methodology ensures that the...
Continue readingEnhancing SailPoint IAM Programs through Effective Monitoring and Administrator Console Usage
A key characteristic of mature SailPoint-enabled Identity and Access Management (IAM) programs is effective production monitoring. Several out-of-the-box tools and reports are available within IdentityIQ to help monitor your production environment. One such tool that is often overlooked is the Administrator Console. In this blog post, we will discuss how to leverage the Administrator...
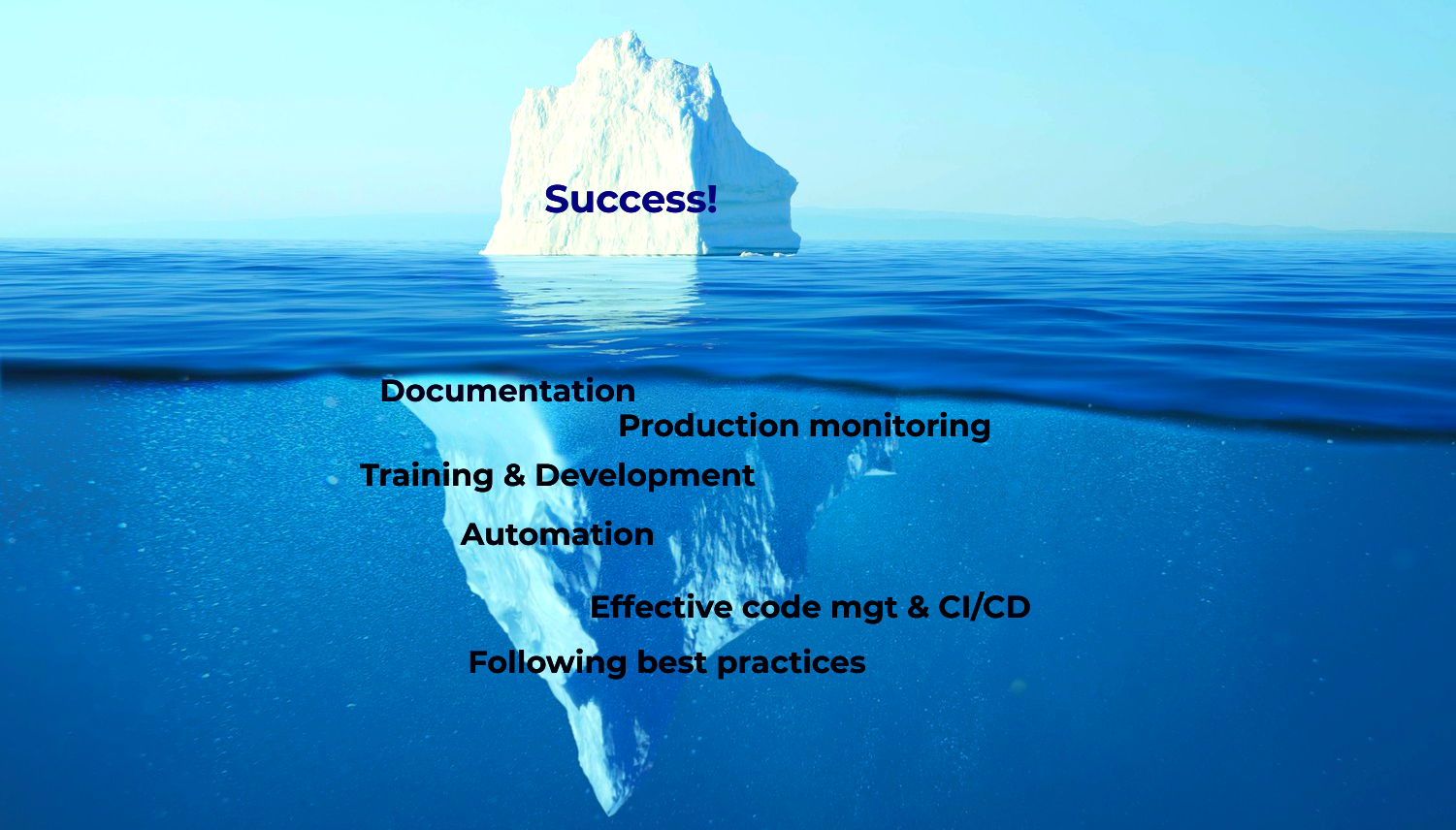
Continue readingIAM Program Transformation – The Success Iceberg
The success iceberg image is a fascinating illustration that answers a question many IAM professionals have in mind: “Why are some IAM programs so robust and mature, while others are not?” As an IAM professional, you might often find yourself putting out fires instead of focusing on more strategic work. However, with effective IAM...
Continue readingEffective Non-Human Account Management in SailPoint IdentityIQ
Non-human accounts are essential for automation in today’s service-oriented and cloud-based IT environment. However, many IAM teams face challenges in managing these accounts. In this blog post, we explore the core design principles for implementing effective non-human account management in SailPoint IdentityIQ, focusing on automation, auditability, and ease of management. Core Design Principles for...
Continue readingThe Importance of Systems in IAM Program Success
I once read that those who fail and those who succeed start out with the same goals. In the same way, successful and failed IAM programs often start with the same goals. So, what makes the difference in achieving IAM program success? The answer lies in the systems implemented, which include processes, tools, people,...
Continue reading3 Key Reasons for Chaotic IAM Environments and How to Stabilize Them
It’s common to assume that chaotic IAM systems and processes are unique to your environment, especially after investing heavily in external consultants, managed services, staffing, and additional tools. However, stable SailPoint IAM environments are less common than chaotic ones, leading IAM leaders to accept chaos as the norm. When asked about the problem, many...
Continue readingEssential Traits for Successful IAM Project Managers
IAM project managers are critical to the success of any IAM project. They are responsible for managing and overseeing the day-to-day operations of the project. In addition to the core project activity and resource planning, it is the responsibility of the IAM project manager to: Understand the goals and priorities of the project –...
Continue readingWhy Identity and Access Management Programs Fall Short
Identity and Access Management (IAM) governance plays a crucial role in every business, yet many organizations struggle to achieve the expected results from their IAM programs. In this blog post, we will discuss two common reasons why IAM programs fail to meet their objectives, and what you can do to address these issues. Two...
Continue readingEffective IAM Migration: Principles and Best Practices
IAM migrations have become an increasingly common practice, particularly as companies embrace a remote workforce model. I have actively guided many of my clients in transitioning from one IAM platform to another, often moving from legacy home-grown tools to more standardized enterprise IAM tools. Here are a few strategies for executing successful IAM migration...
Continue reading